Ex Libris Risk Management Policy 1.2
Version 1.2
Purpose
Ex Libris, a ProQuest company, proactively strives to maintain the security and integrity of Ex Libris information and systems. Reliable and accurate information and systems are critical business assets that will be protected. The purpose of the Risk Management Policy is to provide a methodology for identifying and managing risks so that all risks are addressed, controlled or mitigated.
Scope
This policy applies to all Ex Libris employees or those representing Ex Libris.
Policy Statement
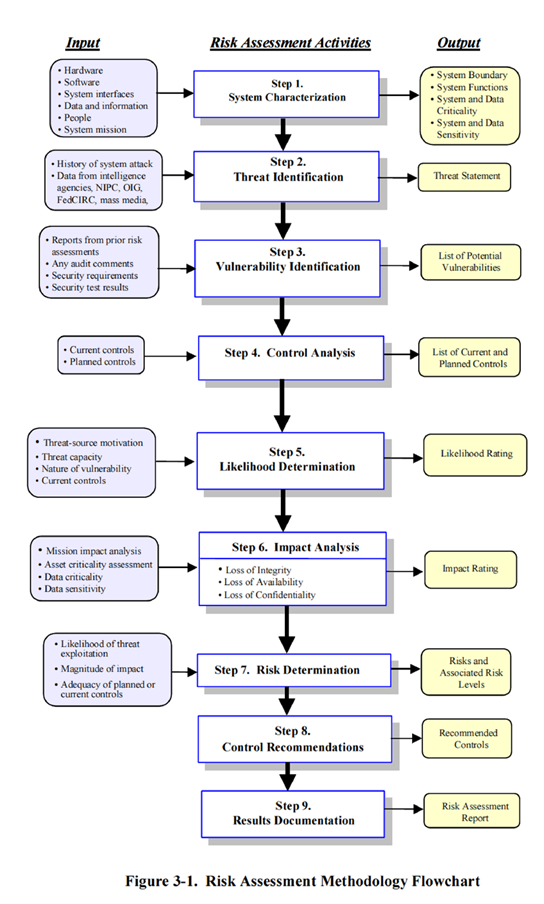
Ex Libris will conduct a risk assessment based on NIST on an annual basis to meet regulatory and contractual requirements.
Reference Documents
Procedure
Roles and Responsibilities
1. Senior Management
1.1. Approves company risk management policies and top enterprise risks.
1.2. Ensures the development of risk management program within the company.
1.3. Allocates resources to implement risk management programs and activities.
1.4. Ensures that, where appropriate, employees receive training in risk management.
2. Enterprise Security Risk Management Committee (The Committee)
The Enterprise Security Risk Management Committee oversees a coordinated approach to assessing and responding to risks that affect the achievement of Ex Libris objectives, led by the Chief Information Security Officer (CISO).
The Committee provides a dedicated forum for advancing risk management and for monitoring the overall effectiveness of the Ex Libris risk management efforts. The Committee approves all risk management policies and then recommends them to the Senior Management for final approval.
The management committee is comprised of Ex Libris’ individuals with decision-making authority who are appointed by Ex Libris’ CISO with the responsibility of assisting in the process described within this document.
The Enterprise Security Risk Management Committee will consist of representatives from the following areas:
- Chief Information Security Officer (CISO) - Team Lead
- Privacy and Regulation Officer & DPO
- Cloud Operation Group (COG)
- Cloud Engineering Group (CEG)
- BU Development
- Global Support Organization (GSO)
- External consultant (upon need)
3. Business Unit Manager
3.1. Participates in risk assessment and control activities.
3.2. Identifies employees to participate, where appropriate, in risk management.
3.3. Monitors the ongoing effectiveness of risk control strategies.
1.4. Chief Information Security Officer (CISO)
4.1. Leads the Risk Management activities.
4.2. Responsible for a comprehensive risk management program, which entails proposing risk vision, strategy, policies, and philosophy regarding risk tolerance to executive management.
4.3. Reports to Senior management.
4.4. Responsible for ensuring the consistent implementation of the Ex Libris risk management program throughout Ex Libris through risk management training and consulting.
4.5. Develops, administers, and helps interpret the Risk Management Policy.
1.5. All Employees
5.1. Responsible for risk management at Ex Libris.
5.2. Make and support risk-informed decisions. Notify supervisor or the Chief Information Security Officer (CISO) so that immediate action may be taken as needed.
Ex Libris Risk Management Process
- Discussions will be held initially with internal and external stakeholders regarding risks that concern each stakeholder or Ex Libris as a whole.
- The internal, external, and risk parameters to be evaluated will be identified and documented so that the scope and risk criteria for the annual process are clearly defined.
- Risks based on events that might enhance, prevent, degrade, or delay the achievement of the objectives for the fiscal year will be identified.
- The cause and/or sources of each risk, its associated consequences (both positive and negative), the likelihood of occurrence, along with the existing controls and their effectiveness will be documented.
- Risk analysis will then be performed. For risks that exceed the Company’s risk tolerance criteria, risk mitigations will be identified and prioritized.
- For risks considered ‘unacceptable,’ mitigations will be considered and implemented as appropriate. Risks that do not have reasonable mitigations available will be discussed by The Committee to determine how to address unacceptable risks. Decisions made by The Committee will be documented.
- The following will be reviewed as part of the process: Lessons learned from events, incidents, changes, and trends
- Changes in the external and internal circumstances including changes to the risk itself
- Risk controls and treatment measures previously implemented to ensure that they are effective in both design and operation
- Emerging risks
Classification of Risk Components
All risks documented in the risk register will be labeled based on one of the four criteria listed below:
Confidentiality – ensuring that information is only accessed as authorized.
Integrity – ensuring that system functionality and the information generated by the system is reliable and has not been changed without authorization.
Availability – ensuring that systems and information are available when needed.
Accountability – ensuring that all users (customers, staff, and third parties) can be identified and are held responsible for actions performed to the system or information.
All risks identified will be scored from Low to High based on the relevance and likelihood of the risk.
Risk-Informed Decision-Making and Operations
Organizational units will include the risk management process into their business operations and processes to ensure that risks are managed effectively.
Criteria for accepting risk
Following full analysis and evaluation of risks, low and information level residual risks are considered an acceptable level of risks as long as the residual risk is managed, reviewed, and where appropriate treatments plans are adjusted.
External Audit
Ex Libris Chief Information Security Officer (CISO) will lead audits conducted by an independent external audit group to validate that the risk management process is working as defined in the policy and that mitigating measures in place to address identified risks are working as intended.
Terms and Acronyms
1. Risk: The effect of uncertainty on achievement of objectives. An effect is a deviation from the expected positive and/or negative. Risk is often expressed in terms of a combination of the consequences of an event (including changes in circumstances) and the associated likelihood of occurrence.
2. Risk Assessment: The overall process of risk identification, risk analysis, and risk evaluation.
3. Risk Tolerance: Measure of the level of risk which an individual or company is willing to accept without further treatment.
4. Risk Management: Strategic business discipline that supports the achievement of an organization's objectives by addressing the full spectrum of its risks and managing the combined impact of those risks as an interrelated risk portfolio. Risk management provides a disciplined process for managing risk and seeks to embed this discipline in existing business processes.
5. Business Impact Analysis (BIA): Documents and analyzes the consequences of disruption of a business function or process.
Risk Management Policy Review
This policy will be reviewed at least annually by the CISO to ensure that the policy is followed and is still relevant.
Enforcement
Failure to comply with this policy may result in disciplinary action, up to and including termination as outlined in the Disciplinary Policy
Record of Changes
| Type of Information | Document Data |
|---|---|
|
Document Title: |
Ex Libris Risk Management Policy |
|
Document Owner: |
Tomer Shemesh - Ex Libris Chief Information Security Officer (CISO) |
|
Approved By: |
Barak Rozenblat - VP Cloud Services |
|
Release Date: |
Apr 28, 2019 |
|
Reviewed & Revised: |
Sept 21, 2020 |
Revision Control
| Version Number | Nature of Change | Date Approved |
|---|---|---|
|
Initial version |
Apr 28, 2019 |
|
|
Review and update - Ellen A |
Apr 23, 2020 |
|
|
1.2 |
Review and update - Tomer S |
Sept 21, 2020 |
Document Distribution and Review
The document owner will distribute this document to all approvers when it is first created and as changes or updates are made. This document will be reviewed and updated annually or upon written request by an approver or stakeholder. Questions or feedback about this document can be directed to the owner or a listed approver.

