Using LDAP for User Authentication
If you are working with Primo VE and not Primo, see Supporting LDAP.
LDAP (Lightweight Directory Access Protocol) is an application protocol for accessing and maintaining distributed directory information services over an IP network. Directory services may provide any organized set of records, often with a hierarchical structure. The usage referred to here is the authentication of user records. The following steps describe the interaction between the user, Primo, and the LDAP server to provide authentication and authorization:
-
The user invokes the sign-in option in Primo.
-
Primo displays the Primo login page.
-
The user enters his or her credentials.
-
Primo sends the user’s credentials in a secured authentication request to the LDAP server.
-
The LDAP server sends a response to Primo indicating whether the user has been authenticated.If the user has been authenticated, the response will also include user information. Otherwise, an error will display on the Primo login page.
-
If the user has been authenticated and the user information method is LDAP, Primo will use the user information sent by the LDAP server and log the user in. If a different method is used to provide user information, Primo will use this method to retrieve user information and log the user on to Primo.
If you need to authenticate against multiple LDAP servers, define multiple login profiles and then define a cascading login profile.
To configure Primo to use LDAP authentication:
-
Gather the necessary information about your LDAP server.
-
Open the User Authentication Wizard page (Primo Home > Ongoing Configuration Wizards > User Authentication Wizard).
-
Create a new login profile. The Login Profile page opens. For more information on creating login profiles, see The Primo Authentication Manager.
-
Select LDAP from the Select Authentication Method drop-down list..
The LDAP authentication parameters appear on the page.
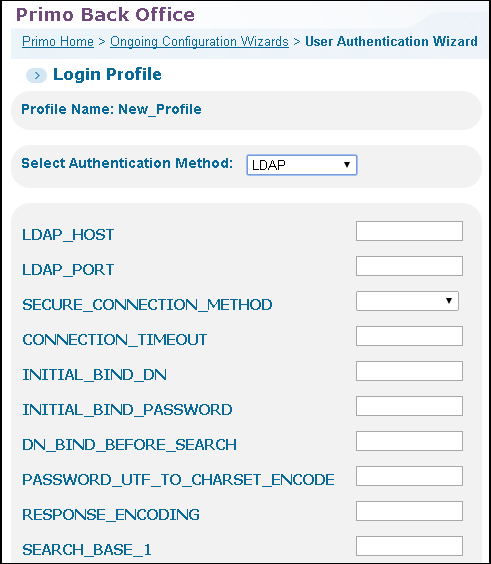 LDAP Login Profile Page (1 of 2)
LDAP Login Profile Page (1 of 2)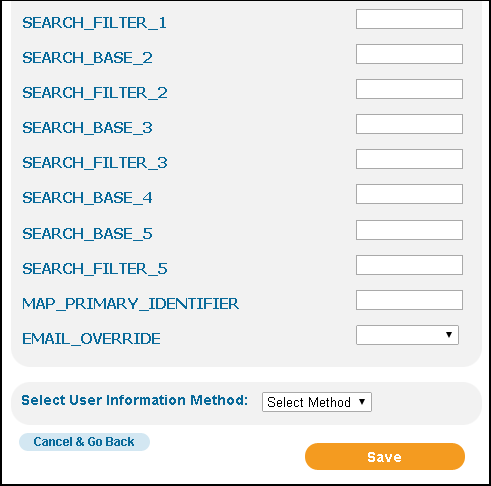 LDAP Login Profile Page (2 of 2)
LDAP Login Profile Page (2 of 2) -
Use the following table to configure the LDAP authentication parameters:
LDAP Configuration Parameters Parameter Description LDAP_HOST(Required) The host name of the remote LDAP server.LDAP_PORT(Required) The port number of the remote LDAP server.SECURE_CONNECTION_METHOD(Required) Select either LDAP secure mode or Transport Layer Security (TLS) to provide an encrypted connection.SSL connections must be secured with a certificate issued by a recognized certificate authority (such as Comodo, Verisign, or Thawte). Use of TLS requires LDAP version 3 or later.CONNECTION_
TIMEOUTThe timeout value in milliseconds.The default value is 60000 (one minute) for the connection timeout.INITIAL_BIND_DNThe full DN (distinguished name) for the initial bind.INITIAL_BIND_
PASSWORDThe DN password for the initial bind.DN_BIND_BEFORE_
SEARCHSpecify the DN when you want to use dynamic password binding instead of a hard-coded password for the initial bind.RESPONSE_ENCODINGIndicates whether to encode the LDAP response before sending it back to the calling application. The only possible value is UTF8.SEARCH_BASE_1 - SEARCH_BASE_5Enter the full path search in the LDAP directory tree to the user. The system searches the LDAP tree to locate the user’s record based on the Search base and Search filter.At least one SEARCH_BASE and SEARCH_FILTER pair must be defined.The SEARCH_BASE and SEARCH_FILTER parameters can be repeated to search in more than one tree. If the results of the SEARCH_BASE and SEARCH_FILTER pair are not unique (or a zero-size result), the search step is repeated for the next provided SEARCH_BASE and SEARCH_ FILTER pair.SEARCH_FILTER_1 - SEARCH_FILTER_5Enter the parameter by which you want to filter the results to return only one object.At least one SEARCH_BASE and SEARCH_FILTER pair must be defined.The system searches the LDAP tree to locate the user’s record based on the SEARCH_BASE and SEARCH_FILTER pair. (See the note for the SEARCH_BASE field.)MAP_PRIMARY_
IDENTIFIERDefines the LDAP user attribute that should be used as the user’s unique ID. If this field is not specified, the LDAP default is used.EMAIL_OVERRIDEThe valid values are True and False (default).If set to True, the email returned with the user information will always override the email stored in the user’s profile in Primo. -
Select ALMA (see Alma Information Request Fields), ALEPH (see Aleph Information Request Fields), or LDAP from the Select User Information Method drop-down list. The selections for the user information method is based on the ILS that you are using.
-
Select Save to save your LDAP profile and to return to the Login Profiles page.
-
Edit your new LDAP profile. The Login Profile page will now include the Attributes Mapping button.
The Attributes Mapping button displays only when the user information method has been selected and saved.
-
If you are using Alma for user information, skip this step. Otherwise, select Attributes Mapping to map the user attributes that are associated with the selected type of user authentication. For more information, see Attribute Mapping.
-
Select Save to save your profile and to return to the list of profiles on the Login Profiles page.

